Dos and DDos attack
Step 1: Block their IP address. This is assuming that this is a DoS attack (coming from 1 IP address.). Use tools like Wireshark to see where this attack is coming from. Then use online tutorials on how to block IP addresses on your firewall. Block the attacker on any P2P (peer to peer) applications (like Skype) so they cannot find your IP.
How To Ddos Using Cmd Stanley Lepaso
Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks are malicious attempts to disrupt the normal operations of a targeted server, service, or network by overwhelming it with a flood of Internet traffic. DoS attacks accomplish this disruption by sending malicious traffic from a single machine — typically a computer.
How to Detect and Analyze DDoS Attacks Using Log Analysis Loggly
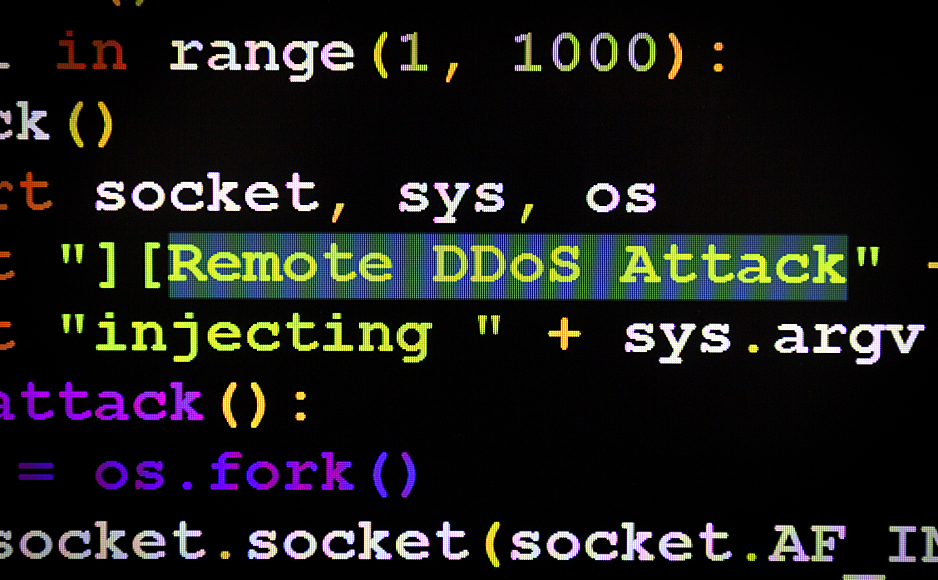
Best DDoS Attack Script Python3, (Cyber / DDos) Attack With 56 Methods. A versatile command and control center (CCC) for DDoS Botnet Simulation & Load Generation. bot ddos dos bots botnet simulation ccc denial-of-service ddos-tool commandandconquer botnets ddos-attack-tools ddos-attack attack-simulator commandandcontrol attack-simulation

Ddos Attack .rDos. & CMDBy AxY YouTube
These commands, combined with the previously mentioned ones, offer a comprehensive toolkit for preventing and stopping DDoS attacks at the application layer. Implementing these commands and adopting a proactive defense approach will enhance your network security and resilience against DDoS threats.

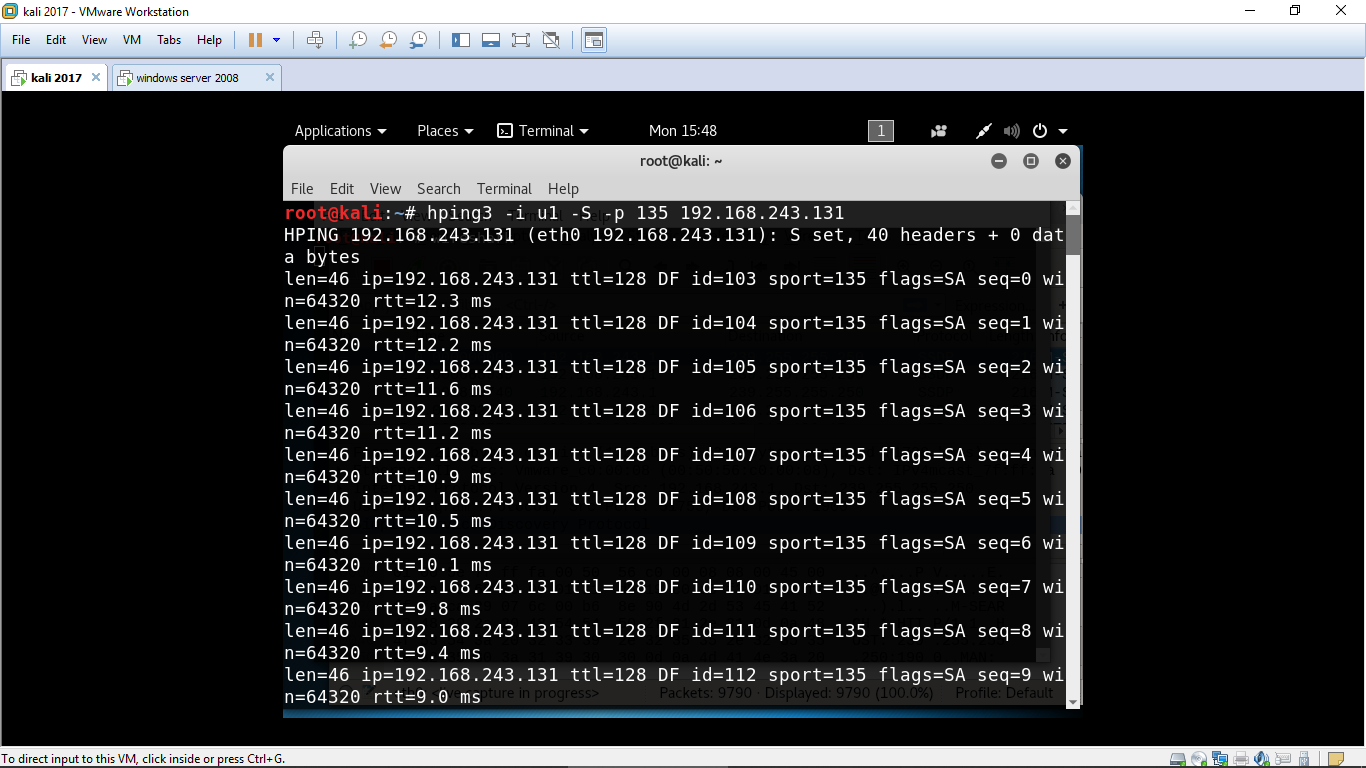
Johny Blog DDoS attack using hping Command in Kali Linux
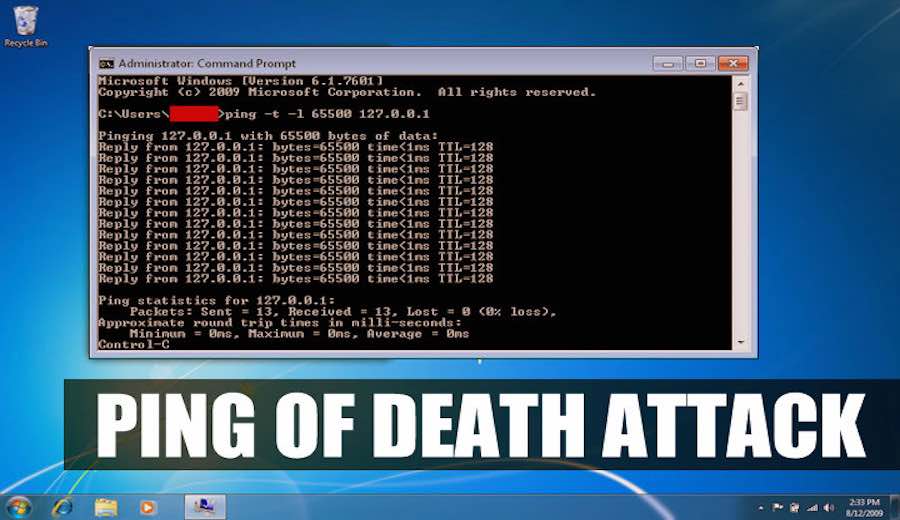
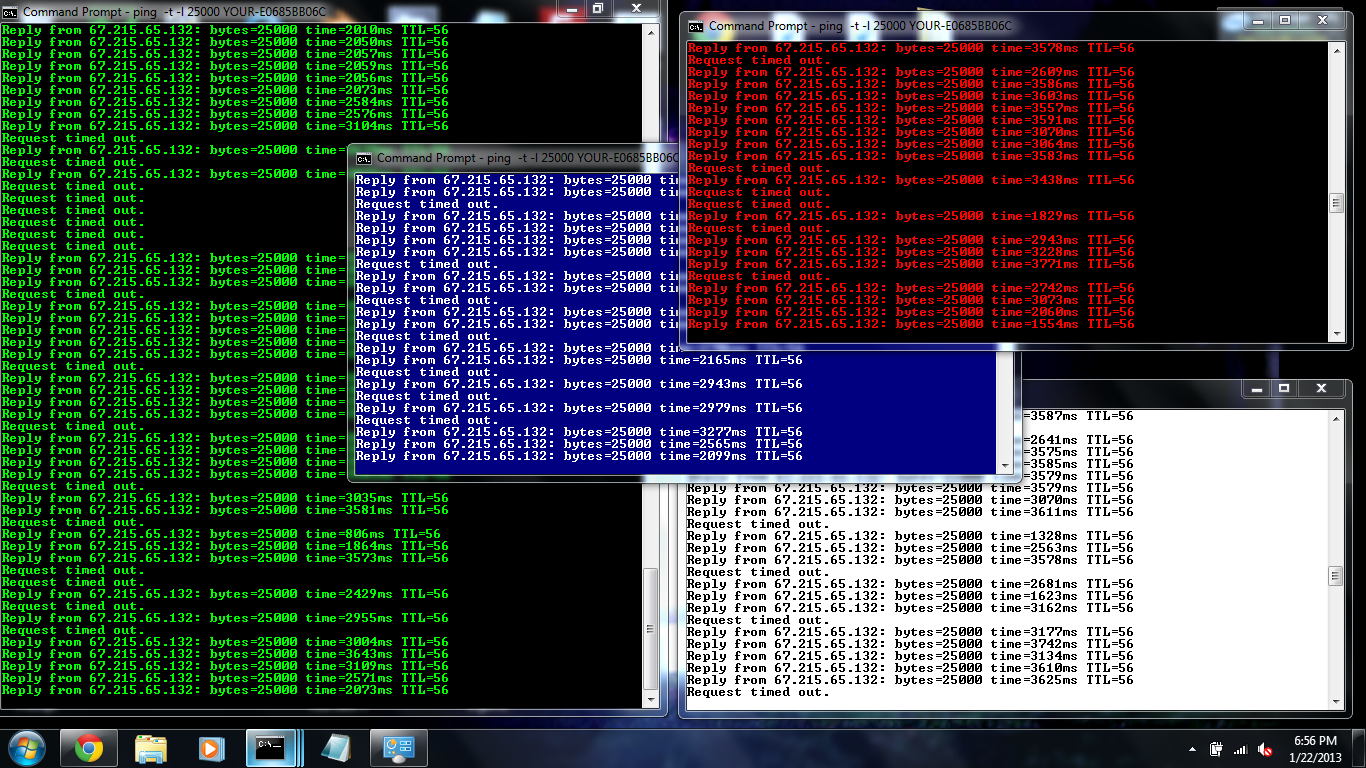
While most modern operating systems are no longer vulnerable to Ping of-Death attacks, a large ping flood using normal-sized packets can still be used to achieve denial-of-service. Technical Example of a Ping Flood. A ping flood can be initiated using a simple ping command from the command line. For example: ping -t
How To Perform Ping of Death Attack Using CMD And Notepad (Just For Learning)
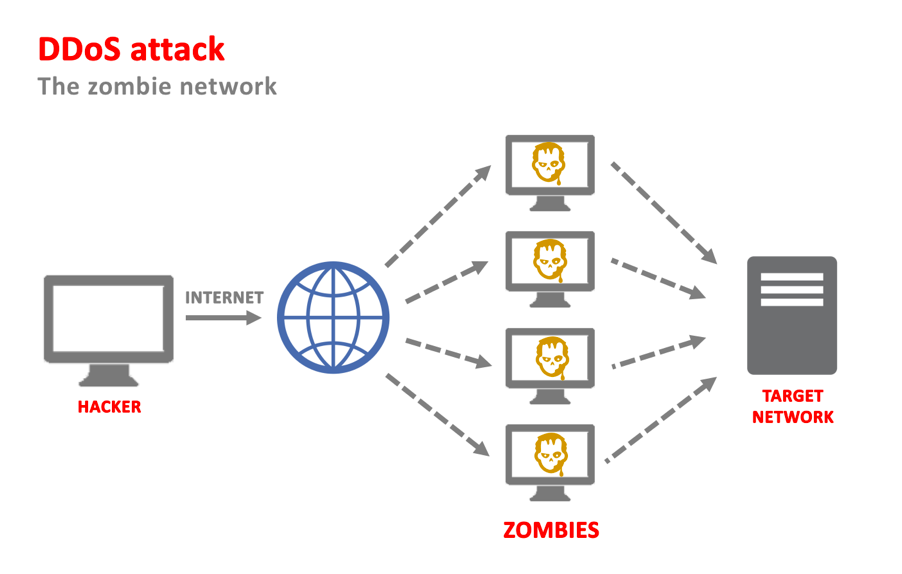
A distributed denial-of-service (DDoS) attack is a malicious attempt to disrupt the normal traffic of a targeted server, service or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic. DDoS attacks achieve effectiveness by utilizing multiple compromised computer systems as sources of attack traffic.
How to perform DDos attack using CMD DR Hacker4U
Unlike in ransomware attacks` case, there are no fast-financial gains expected when planning a DDoS attack. However, it might happen that hackers try to extort a company by using DDoS as a weapon. Here below are the reasons why hackers launch DDoS attacks: DDoS as an Obfuscation Technique. In many cases, hackers use DDoS attacks as smokescreens.
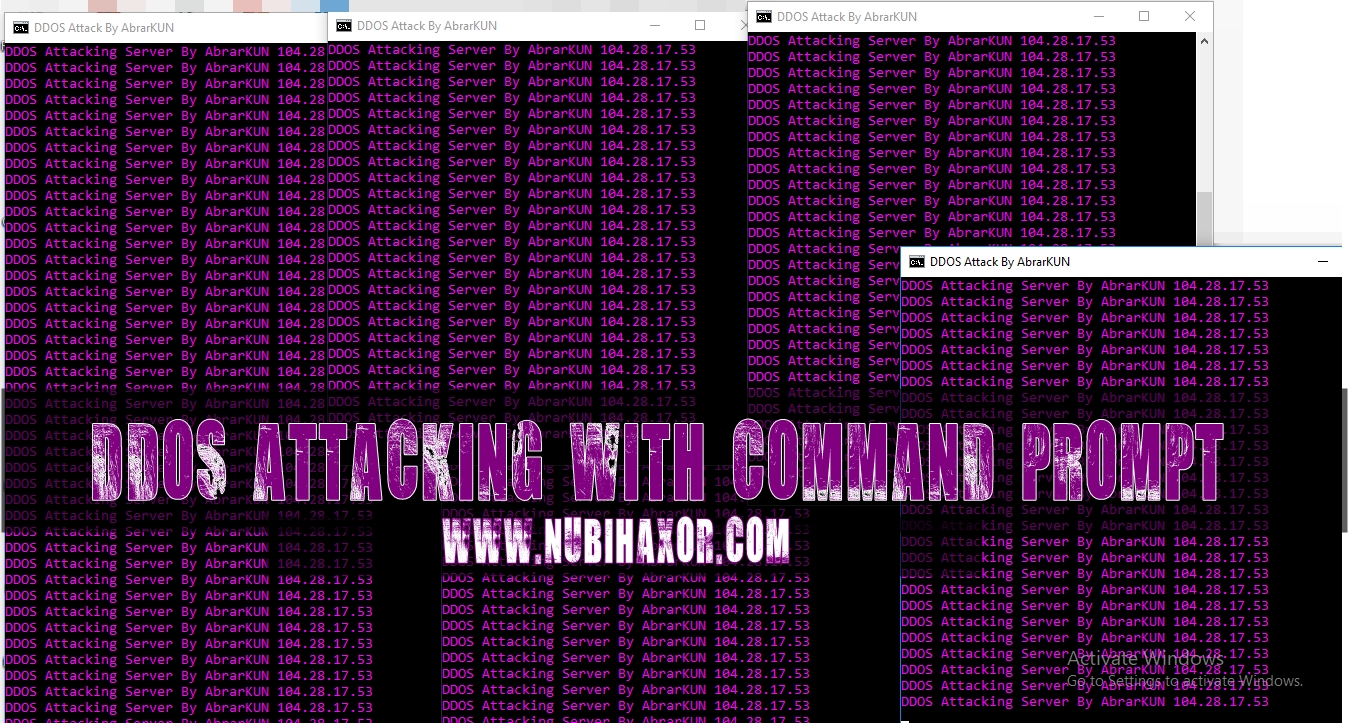
Tutorial Cara Mudah DDOS Attack Hanya Dengan Program Prompt
Discover how a ping of death command works and how to protect your organization from ping of death and DDoS attacks. The ping of death is a form of denial-of-service (DoS) attack that hackers use to crash or freeze computers, services, and systems.. Attackers use ping commands to develop a ping of death command. They can write a simple loop.
Ddos Attack Cmd news word
A Command and Control attack is a type of attack that involves tools to communicate with and control an infected machine or network. To profit for as long as possible from a malware attack, a hacker needs a covert channel or backdoor between their server and the compromised network or machine. The cybercriminals server, whether a single machine.
How To Make Ddos Attack With Cmd Image to u
Open the Notepad app. Copy and paste the following commands. :loop. ping
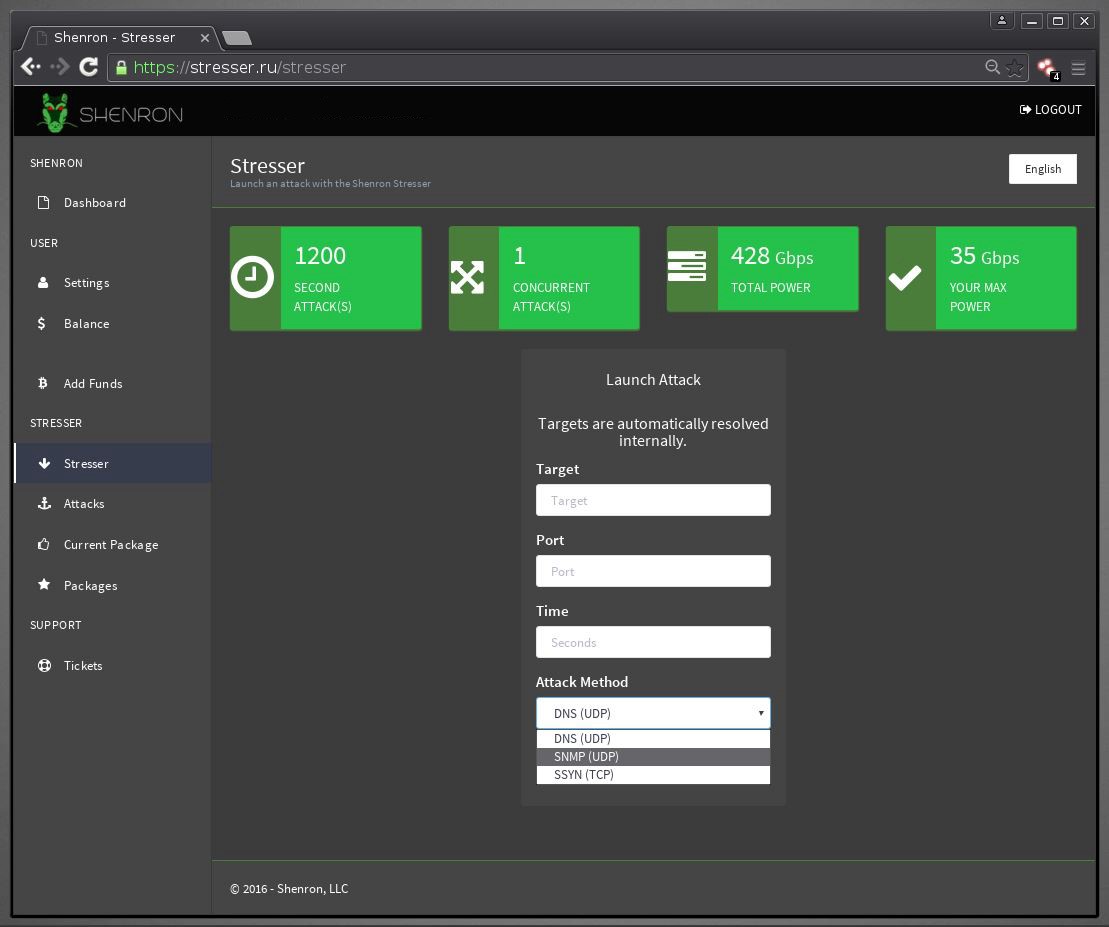
DDoS Attacks via DDoS as a Service Tools
April 19, 2022. (Image: Shutterstock/Hernan E. Schmidt) Command and control attacks allow hackers to take over entire networks or turn individual PCs into an army of bots they can use for their.

How To Ddos with CMD (Beginners) YouTube
A dedicated server with DDoS protection is prepared to continue working without disruptions in availability. Use the route command to block the attacker's IP address. sudo route add [ip-address] reject. Note: The route command is part of the net-tools package. To install it on Ubuntu, type:
Ddos Attack Cmd news word
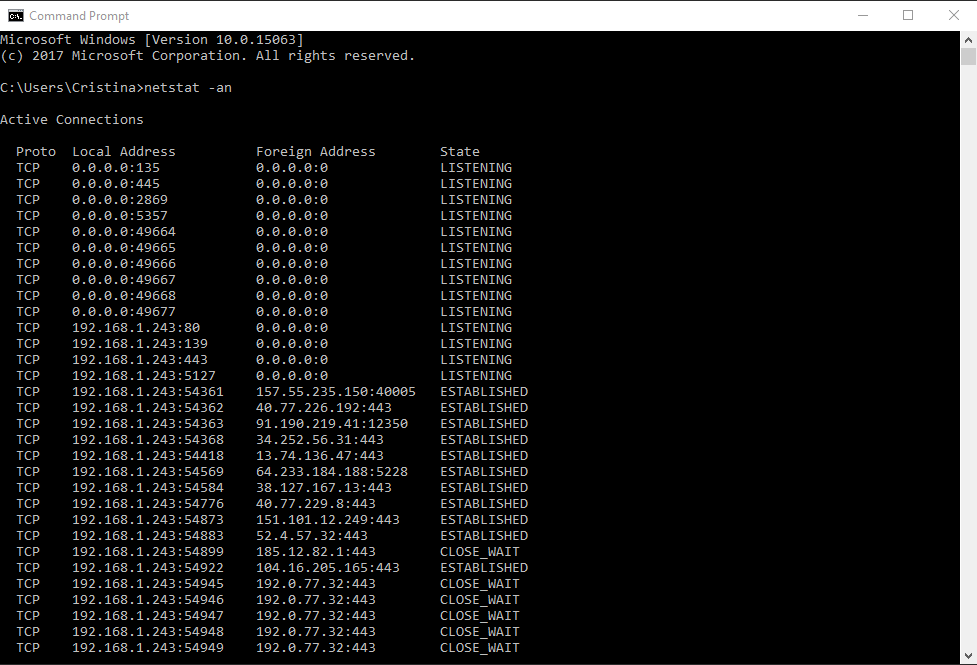
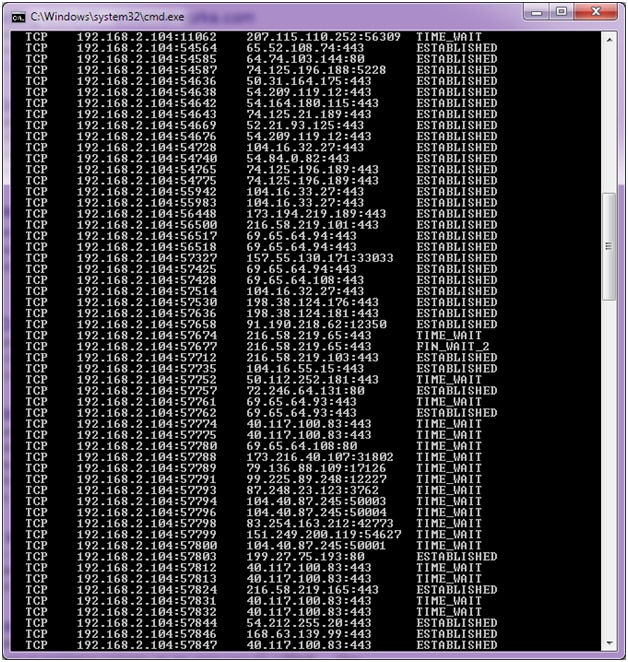
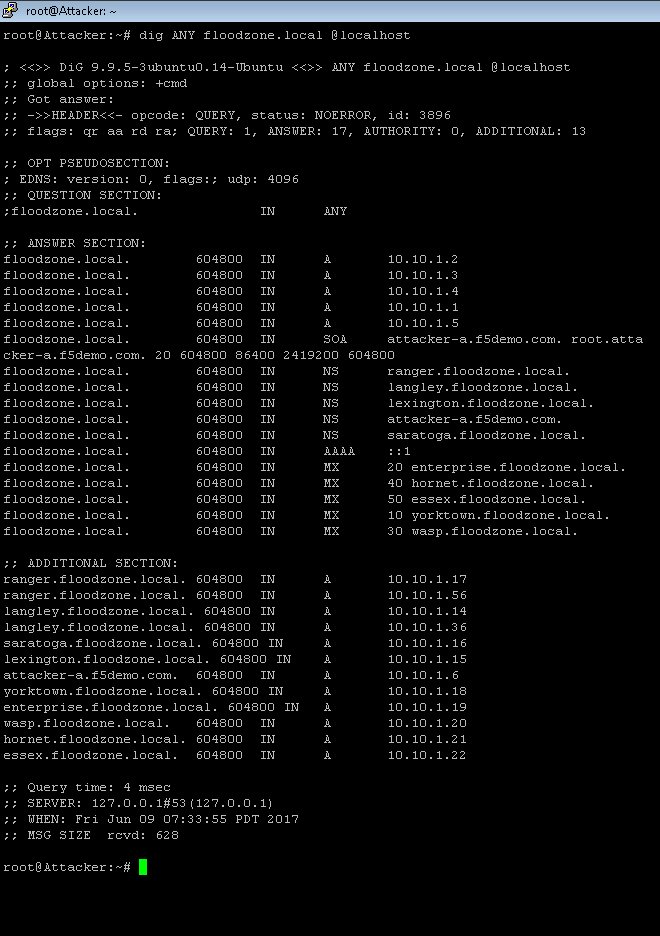
Useful in detecting a single flood by allowing you to recognize many connections coming from one IP. #netstat -n -p|grep SYN_REC | wc -l. To find out how many active SYNC_REC are occurring on the server. The number should be pretty low, preferably less than 5. On DoS attack incidents or mail bombs, the number can jump to pretty high.
SIMPLE DDoS Tools C.I.H.C Secret Channel
Open the command prompt on the target computer. Enter the command ipconfig. You will get results similar to the ones shown below. For this example,. DDoS attack is an escalated form of a DoS attack where the malicious traffic comes from multiple sources - making it harder to stop the attack simply by blocking a single source..
Dos/DDos Attacks InfosecTrain
ping www.google.com -t. Note: Replace www.google.com with the website on which you want to perform the DDoS attack. c. You will see the IP address of the selected website in the result. Note: IP address will look like: xxx.xxx.xxx.xxx. 3. After getting the IP address, type the below command in the command prompt.
Powerful ddos attack tool peacedarelo
Denial-of-service Attack - DoS using hping3 with spoofed IP in Kali Linux. In computing, a denial-of-service ( DoS) or distributed denial-of-service ( DDoS) attack is an attempt to make a machine or network resource unavailable to its intended users. Although the means to carry out, the motives for, and targets of a DoS attack vary, it.